North Korea stories

Google links axios attack to suspected North Korean actor
This month
#
devops
#
advanced persistent threat protection
#
supply chain
Google says the axios npm supply chain attack was linked to suspected North Korean actor UNC1069, raising fears for Australian and New Zealand firms.

North Korean operatives target Australian jobs, DTEX warns
Last month
#
hcm
#
advanced persistent threat protection
#
physical security
DTEX warns North Korean operatives are using false identities to secure Australian tech jobs, with some applicants aided by AI and deepfakes.

Cyber extortion tops 2025 attacks as AI risks escalate
Last month
#
data protection
#
ransomware
#
mfa
Cyber extortion has overtaken email scams as the top 2025 attack, as AI-powered threats grow and financial firms become prime targets.

AI-fuelled cyber attacks hit in minutes, warns CrowdStrike
Tue, 24th Feb 2026
#
saas
#
ransomware
#
cloud security
AI is fuelling a surge in cyber attacks, with CrowdStrike warning criminals now move from breach to lateral movement in under 30 minutes.
Healthcare tops cyber attacks on Australian OT & IoT
Fri, 20th Feb 2026
#
ransomware
#
manufacturing
#
iot security
Healthcare is now the prime target for OT and IoT cyber attacks in Australia, as security alerts per organisation surge to third globally.

Okta warns of North Korean fraud in remote tech hiring
Fri, 13th Feb 2026
#
data protection
#
ransomware
#
hcm
Okta warns North Korean operatives are landing remote tech jobs with stolen and synthetic identities to fund the regime and enable cyber attacks.

Google warns of AI model theft & state-backed misuse
Thu, 12th Feb 2026
#
malware
#
surveillance
#
cloud security
Google flags surging attempts to steal AI models as state-backed hackers weaponise Gemini for phishing, intel gathering and malware support.
Hackers ditch noisy ransomware for stealthy data theft
Thu, 12th Feb 2026
#
firewalls
#
data protection
#
dr
Hackers are abandoning noisy ransomware to quietly steal data, as a report finds 80% of top attack techniques now focus on evasion.

CrowdStrike splits LABYRINTH CHOLLIMA into three units
Fri, 30th Jan 2026
#
malware
#
manufacturing
#
crypto
CrowdStrike has split North Korea-linked LABYRINTH CHOLLIMA into three units, two for crypto theft and one for industrial espionage.

Google disrupts IPIDEA's global hijacked device network
Thu, 29th Jan 2026
#
malware
#
firewalls
#
data protection
Google has dismantled IPIDEA's vast residential proxy network, which hijacked millions of consumer devices for global cyber operations.

Team Cymru & Filigran integrate Pure Signal with OpenCTI
Fri, 16th Jan 2026
#
firewalls
#
ransomware
#
network security
Team Cymru and Filigran link Pure Signal and Scout with OpenCTI to enrich threat investigations, automate hunts and deepen global context.
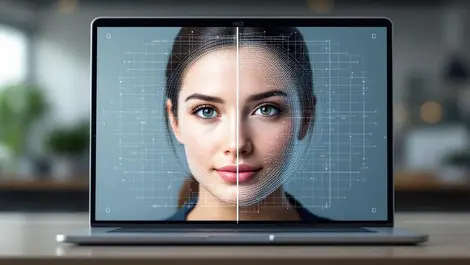
iProov, HYPR join forces to combat AI-driven deepfakes
Fri, 9th Jan 2026
#
surveillance
#
biometrics
#
mfa
iProov and HYPR integrate liveness checks with passwordless login to stop deepfake workers infiltrating enterprises at onboarding.

How identity verification could have stopped a $300M Crypto scam
Wed, 24th Dec 2025
#
malware
#
uc
#
ransomware
North Korean hackers stole USD $300M via fake Zoom calls; robust identity checks could have broken the scam's chain of trust.

Exclusive: Google on AI-powered attacks & cyber threats in Australia
Mon, 10th Nov 2025
#
malware
#
phishing
#
advanced persistent threat protection
AI-driven cyber threats are escalating in Australia, with criminals deploying deepfakes and malware that evolves to bypass security, warns Google's Andrew Aston.

Google warns of AI misuse in new GTIG threat report
Thu, 6th Nov 2025
#
malware
#
phishing
#
email security
Google's threat team warns that hackers are now using AI to create self-modifying malware and evade defences.

North Korean group uses blockchain to launch advanced malware
Fri, 17th Oct 2025
#
malware
#
crypto
#
blockchain
A North Korean group has used blockchain-based EtherHiding to secretly deploy malware, targeting developers in tech and cryptocurrency sectors worldwide.

Google Cloud warns backup systems face rising cyber threats
Wed, 20th Aug 2025
#
malware
#
ransomware
#
mfa
Google Cloud's new report warns rising cyber threats target backup systems, with nearly half of cloud attacks exploiting weak credentials and misconfigurations.

Australia urged to unify cyber defences as threats intensify
Tue, 8th Jul 2025
#
advanced persistent threat protection
#
risk & compliance
#
data privacy
Australia is being urged to unify cyber defences and tighten policy as state-backed hackers and cyber crime intensify across key sectors.

North Korean hackers step up phishing attacks on Ukraine government
Wed, 14th May 2025
#
malware
#
cybersecurity
#
proofpoint
North Korean hackers have intensified phishing attacks on Ukrainian government bodies to gather strategic intelligence on the Russian invasion, Proofpoint reports.

Zero-day hackers shift focus to enterprise tech in Google's report
Thu, 1st May 2025
#
firewalls
#
network security
#
breach prevention
Google's GTIG reports 75 zero-day exploits in 2024, highlighting a rising threat to enterprise tech despite a slight overall decrease from 2023.