
WhiteHawk lands 'milestone' $5.9 million cybersecurity contract
Wed, 29th Jul 2020
WhiteHawk Limited has been contracted by a US federal government chief information security officer (CISO) to implement WhiteHawk's Cyber Risk Radar.
News of the contract resulted in a substantial increase in the company's share price as it soared approximately 50% at time of writing on Tuesday morning — a near 14 month high.
WhiteHawk is the first global online cybersecurity exchange enabling businesses of all sizes to take smart action against cybercrime.
The annual Software as a Service (SaaS) contract is a milestone contract with a Tier 1 client – a key US federal government department.
It will see WhiteHawk generate base revenues of US$580,000 (A$811K) and up to an additional US$600,000 (A$839K), for a total of up to US$1.18 million (A$1.65M) for each year of the contract of $5.9 million in total. This will have a large impact on the company's top line revenue growth.
WhiteHawk will implement its Cyber Risk Radar for the undisclosed US federal government Chief Information Security Officer (CISO).
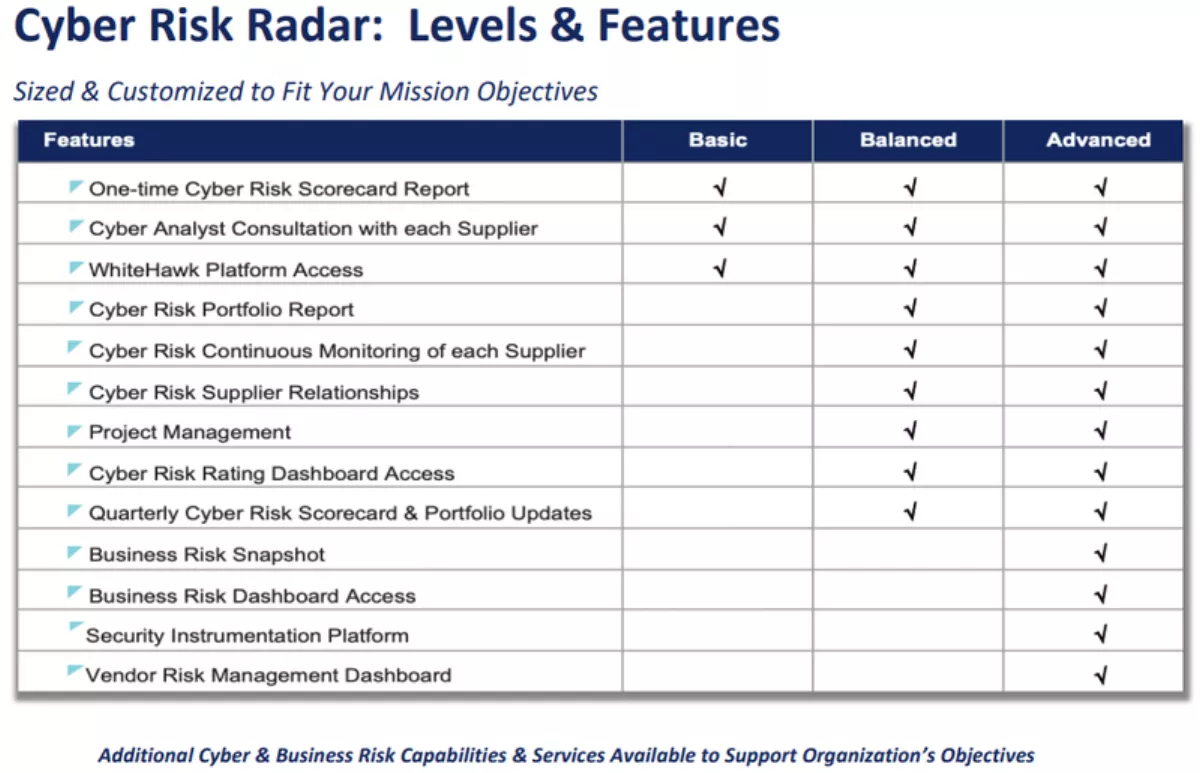
The Cyber Risk Radar is a SaaS subscription that will monitor, identify, and prioritise both cyber and business risks of vendor companies to this US federal government department.
WhiteHawk will provide Cyber Risk Scorecards quarterly, virtually and remotely, for the department's 150 to 300 vendors, via an integrated risk management dashboard.
This is the first US federal contract where WhiteHawk is the Prime Contractor.
Of its three other US federal department CIO contracts, WhiteHawk is a cyber solution sub-contractor to Accenture Federal, SAIC and GuideHouse (formerly PWC Federal).
As this is the first US federal contract where WhiteHawk has been nominated as the Prime Contractor, it is an extremely important development.
Terry Roberts, executive chair of WhiteHawk said of the contract, "After a very successful Proof of Value early last year, now we are putting in place our first 5-year Cyber Risk Radar contract with a sophisticated US government CIO, who will work with us to take the capabilities of our platform and virtual services to the next level.
As Roberts stated, this contract is the result of a Proof of Value that was implemented early in 2019 across 10 vendors for the same US government agency.
Roberts recently told Yahoo Finance that she was a self-confessed "paranoid international risk professional". More importantly, she is a 35-year veteran of the US national security and cyber intelligence community, including as a former Deputy Director US Naval Intelligence, a Department of Defence Senior Executive, and an Executive at the Carnegie Mellon Software Engineering Institute.
WhiteHawk mitigates safety concerns
WhiteHawk demonstrated through automation and subject matter expertise, the status and health of suppliers using global publicly available data sources, AI analytics, and custom Cyber Analytics to assess and report on top risk indicators and vectors, areas that may require prioritised attention.
Because the Cyber Risk Radar approach is externally available data and is non-invasive, WhiteHawk does not require access to internal IT assets and configurations in order to deliver its services.
Rapidly evolving technology had already set cybersecurity up to be a major growth sector, but the sudden COVID-19 driven shift to remote work has brought this sector to the fore quicker than anticipated.
Organisations are vulnerable to malicious attempts to exploit this shift — right as their IT teams are stretched to the max and as they become increasingly dependent on the internet and a remote workforce to operate.
Yet organisations are recognising the need for ongoing risk monitoring and mitigation approach to cybersecurity — now more than ever.
Given the company's market capitalisation of approximately $20 million, there is significant potential upside on offer here as the company continues to sign new partnerships and bring in new revenue streams in this ever changing environment.