What is a DApp and why are they useful?
DApps are an innovative way to make use of a blockchain's capabilities. But it can be tough to find a plain English definition of exactly what they are and how they differ from traditional applications.
What is a decentralised app?
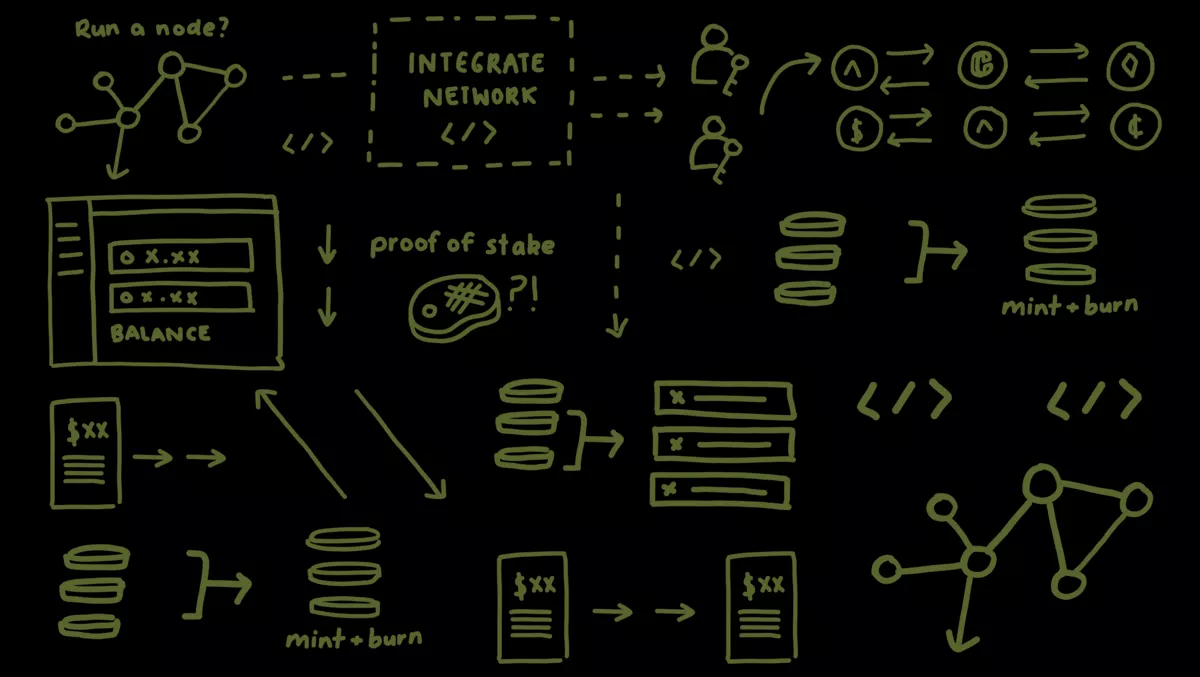
A decentralised app, or DApp for short, is an online application that connects to the blockchain in some way. It typically involves just a small component of the app connecting to the blockchain through a straightforward API. Although DApps are used in the same way as any other software application and can be based on a website or as a mobile app, they are distinct from normal apps:
- Totally or partially decentralised: Some activity and data in a DApp run through a distributed network of machines/nodes, i.e. a blockchain network rather than a centralised server.
- Unkillable: If a significant amount of the DApps data is stored on a blockchain, then they have no single, central point of failure.
Optional extras often associated with DApps:
- Open source: You don't technically have to open source your code to make your DApp, but it's common. It gives your user base complete visibility and trust in your app.
- Data ownership: Many DApps, specifically DApp creators, don't own their users' data. Users are empowered to own their own data, either to share with different DApps or remove it fully from the ecosystem.
- Tokens: Many DApps embrace some form of token, which can be very useful for rewarding your community. With DApps, users' money/rewards can stay in their own wallets.
There is debate over what constitutes a DApp in the purest of senses. The key factor to remember is that DApps are built on a decentralised network.
To understand what makes DApps special, first, we need to dive into how centralised apps work.
How do centralised apps work?
Okay, so we are going super basic here. Please forgive any generalisations. The majority of traditional apps consist of three key functions:
- Interface: Users interact with the app via the front end of a web, mobile or desktop interface.
- Server: Requests from the front end are then passed to a centralised server.
- Database: Data from user actions on the front end (acquired through requests through the server) are collected and stored on a centralised database owned by a single company or individual.
Centralisation provides low-cost hosting, fast running speeds, easy development and a tightly controlled user experience.
However, these advantages come at serious costs, including handing over a significant amount of control to large hosting organisations and becoming a tempting target for hackers. DApps offer an alternative that seeks to solve all these problems and add a bit of social justice to boot.
How do DApps work?
Assuming that the whole DApp is built on the blockchain, we can split a DApp's functionality into three basic stages:
- Interface: The front end is largely the same as a centralised app.
- Smart contract: Smart contracts are the part of the DApp that interacts with the blockchain network. In this basic explanation, the front end communicates with the smart contract using an API (while in reality, this happens via a blockchain wallet).
- Blockchain network: Code run by the smart contract then selects and stores data on the decentralised blockchain network.
The special thing about the DApp is the bottom layer – the blockchain network upon which the entire system runs. Unlike the centralised database, which is owned and controlled by one person (or a multinational conglomerate), the blockchain network is fully decentralised, meaning it is run and seen by every user in the ecosystem.
It's a peer-to-peer system. Every request from the front end of the app filters through every person (node) on the network. They all run the code from the smart contract and store the resulting blockchain data on their copy of the ledger. So everyone has their own record of every transaction that has ever happened on the DApp, allowing maximum visibility and community ownership of data. Mind-blowing right?
Why are DApps an opportunity for developers?
Security, security, security
Data privacy is now a legal and moral requirement for every organisation. The good news is that DApps make the job of securing user data much more manageable.
By running on a distributed blockchain computing system, DApp stored data is not vulnerable to one single point of failure. This makes it structurally much harder (if not impossible) for hackers to steal user data, unlike the centralised storage of big tech companies. On top of that, cryptographic verification methods such as the Zero Knowledge Proof (ZKP) method make it doubly safe for data security.
Resisting censorship
For developers or customers in parts of the world where the government enjoys tighter control over the internet, this is important. There is no single entity on the network which can block users from deploying DApps, reading data, or submitting transactions through the blockchain – meaning your service can carry on regardless of worldwide pressures. Even better, by avoiding building on any of the big company platforms, they are also unable to shut down your app.
Full trust
Everyone can check out and analyse the code run in a DApp, to make sure it's fair and accurate. This way, everyone can see exactly what's happening.
Say goodbye to downtime
Once your smart contract is deployed and set up on the blockchain, you are officially unkillable. The network will always be able to serve clients interacting with the smart contract. Hackers or other malicious parties would have to pay colossal prices to launch denial-of-service attacks on individual DApps.
DApps come with some challenges – naturally – like high computational overheads (which can be addressed by smart designs), a slower network, and the challenge of creating a user-friendly experience. DApps can certainly sound like a daunting new skillset, but with the right tools, adding a pinch of blockchain to your app is straightforward and hugely rewarding.

