General staff don’t get tech jargon - expert says time to ditch it
In a world where massive breaches seemingly surface on a weekly basis, businesses are scrambling to get their cybersecurity up to scratch.
Most of these breaches come from human error, according to Embedded Knowledge co-founder – and co-author of 'From Problem Solving to Solution Design: Turning Ideas into Actions' - J. Eduardo Campos, who asserts there can be a simple solution to many of these instances.
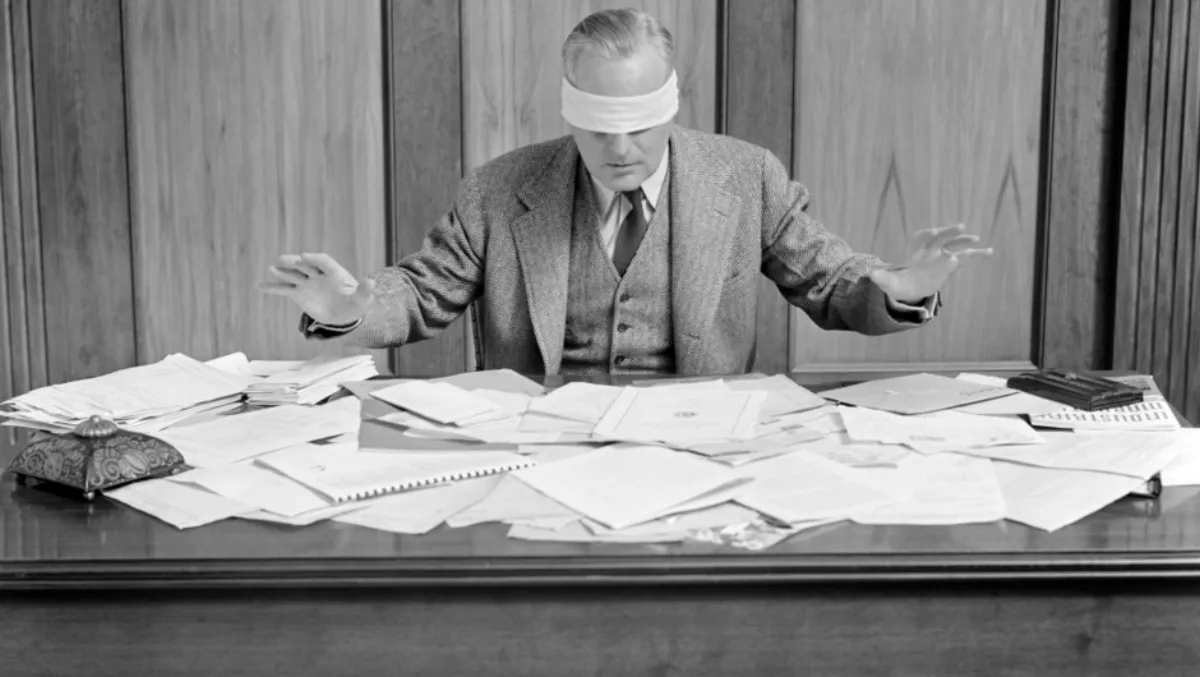
An office memo that tosses around terms like DRM, botnet, FTP, spear phishing and worm could be a quick, easy read for the head of the IT department. But for everyone else in the organisation it may or may not be one big mass of confusion – and with that bewilderment comes potential danger.
"There's a serious gap in communication skills between cybersecurity pros and their general audiences, and it's essential for the people on the IT side to bridge it,'' Campos says.
"Increasingly complex security threats demand that cybersecurity professionals use plain language when they are communicating with those less familiar with tech talk.
Campos says organisations can be vulnerable to hackers even if the staff have been warned about what to look for, simply because the employees don't understand the language behind the warning.
After all, cyber threats aren't just a technology problem - they are a people problem, says Campos, who worked on cyber threats as a former employee of Microsoft.
''People are the weakest link in computer security and many companies don't promote a company philosophy of 'computer security is everybody's business'," Campos says.
In light of this, Campos has a few tips to improve communication between IT and everyone else in the organisation:
- Incorporate this need into the hiring process. When hiring new staff for IT and cybersecurity teams, look for experts who have not only tech skills, but also the skills necessary to comfortably interact socially and clearly communicate in lay terms with all the stakeholders in the organisation.
- Focus on training. Cybersecurity teams can be trained to become solution designers who can connect the dots, Campos says. They can then capture, clarify, and address all stakeholders' concerns, helping them to determine and keep their goals aligned.
- Realize this is an ongoing process. It's important to ensure that the improved communication is sustained over the long haul, and people don't revert to old ways down the road, Campos says.
"Data breaches, data ransom plots, and email hacks intimidate us all. Cybersecurity teams themselves feel hard-pressed enough to prepare themselves for the onslaught of these gremlins, let alone to accomplish the challenging task of communicating to stakeholders about how to mitigate and deal with cybersecurity risks," Campos says.
"But for organizations to keep their information and systems safe, that communication needs to be done, and in a way everyone can understand.

