Digital Credentials stories

Skillsoft data shows surge in AI skills validation
Yesterday
#
e-learning
#
genai
#
ai
Skillsoft data shows a sharp rise in AI learning and validation activity, with benchmark completions up 994% as employers seek proof of practical capability.

Khan TED Institute targets low-cost AI-focused degree
3 days ago
#
edutech
#
e-learning
#
iam
ETS, Khan Academy and TED plan AI-focused higher education model with skills-based progression and corporate backing, aimed at costing under $10,000.

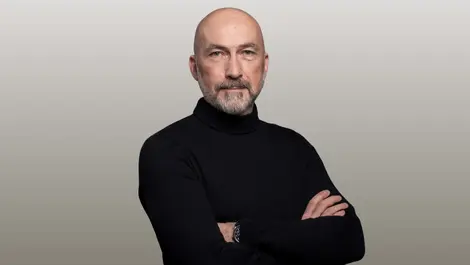
Ledger appoints Ian Rogers to lead AI security push
3 days ago
#
crypto
#
fintech
#
mdm
Ledger names Ian Rogers as Chief Human Agency Officer, putting hardware approval and human oversight at the centre of its AI security push.

Visa & Westpac launch digital fleet payments in Australia
Last week
#
digital transformation
#
crypto
#
fintech
Visa and Westpac to launch mobile wallet fleet payments in Australia, giving businesses real-time controls and wider merchant acceptance from 2026.

Banks issue warning over AI-powered identity fraud risks
Last month
#
data protection
#
surveillance
#
mfa
US banks and regulators are urged to adopt passkeys, mobile driving licences and tougher verification as generative AI fuels deepfake fraud.

Tap into the future: How the University of Sydney transformed campus life with digital ID
Last month
#
edutech
#
data protection
#
digital transformation
University of Sydney swaps ageing plastic cards for tap-and-go digital IDs, transforming access, security and sustainability across campus.

Okta names Dan Mountstephen to lead APJ identity push
Mon, 2nd Feb 2026
#
digital transformation
#
cloud security
#
partner programmes
Okta appoints Dan Mountstephen to steer Asia Pacific and Japan growth, sharpening its identity-led cyber and AI security strategy.

Skillable: hands-on AI training key to 2026 software sales
Wed, 14th Jan 2026
#
saas
#
cx
#
martech
Skillable says hands-on AI labs and scenario-based training will be vital for proving software value and closing complex 2026 deals.

Skillsoft links edX courses to corporate AI skills
Wed, 24th Dec 2025
#
edutech
#
digital transformation
#
e-learning
Skillsoft links edX's university courses to its AI-focused learning platform, tying academic credentials more tightly to corporate skills needs.

Digital wallets & AI threats to reshape ID security
Fri, 19th Dec 2025
#
digital transformation
#
crypto
#
physical security
Digital wallets and decentralised IDs are set to surge by 2026 as AI-driven threats push firms to monitor human and machine identities nonstop.

Standards Australia unveils flexible online training for trades
Fri, 28th Nov 2025
#
iam
#
risk & compliance
#
cybersecurity
Standards Australia launches flexible online training platform offering certified courses to help trades and technical professionals meet compliance and safety standards.

Mortar AI launches MMM Pulse for rapid campaign impact insights
Fri, 14th Nov 2025
#
iam
#
ueba
#
cybersecurity
Mortar AI launches MMM Pulse, a fast, data-light tool giving marketers quick, reliable insights into the true impact of campaigns and channels.
Report shows Mobile Access Control delivers real green savings
Wed, 12th Nov 2025
#
encryption
#
crypto
#
physical security
A study reveals mobile access control reduces environmental impact by over 75% compared to PVC cards, boosting sustainability in security solutions.
Saviynt unveils partner accreditation to boost cloud delivery
Wed, 11th Jun 2025
#
iam
#
cybersecurity
#
enterprise security
Saviynt has introduced its Partner Delivery Excellence Program to recognise and certify partners skilled in implementing its Identity Cloud for improved customer outcomes.

Quishing attacks rise as QR codes pose new cybersecurity risks
Wed, 23rd Apr 2025
#
malware
#
digital transformation
#
physical security
QR code phishing, or Quishing, is on the rise globally, with attacks up 51% as cybercriminals exploit trusted codes to steal data and spread malware.

Gallagher extends digital badge programme to APAC & IMEA
Thu, 6th Mar 2025
#
iam
#
cybersecurity
#
ims global
Gallagher Security has expanded its Digital Badge programme across the Asia Pacific and IMEA regions, recognising skills and achievements through verified credentials.

Exclusive: HID discusses shift towards digital and AI-driven solutions
Wed, 5th Mar 2025
#
surveillance
#
digital transformation
#
biometrics
The security sector in Australia and New Zealand is rapidly shifting towards digital solutions, with HID's Steve Katanas highlighting the role of AI and mobile credentials.

ISACA launches new certification for cybersecurity skills
Thu, 6th Feb 2025
#
advanced persistent threat protection
#
iam
#
cybersecurity
ISACA has launched the Certified Cybersecurity Operations Analyst credential to meet the rising demand for skilled cybersecurity professionals with hands-on experience.

Siemens unveils Apple Wallet access for Building X users
Mon, 13th Jan 2025
#
firewalls
#
digital transformation
#
network security
Siemens Smart Infrastructure has introduced a mobile access feature for Building X Security Manager, enabling users to enter buildings via Apple Wallet integration.

Gen foresees rising AI-driven scams & identity risks by 2025
Thu, 5th Dec 2024
#
physical security
#
email security
#
iam
Gen's cybersecurity predictions for 2025 highlight a surge in identity theft and hyper-personalised scams driven by AI advancements and major breaches.