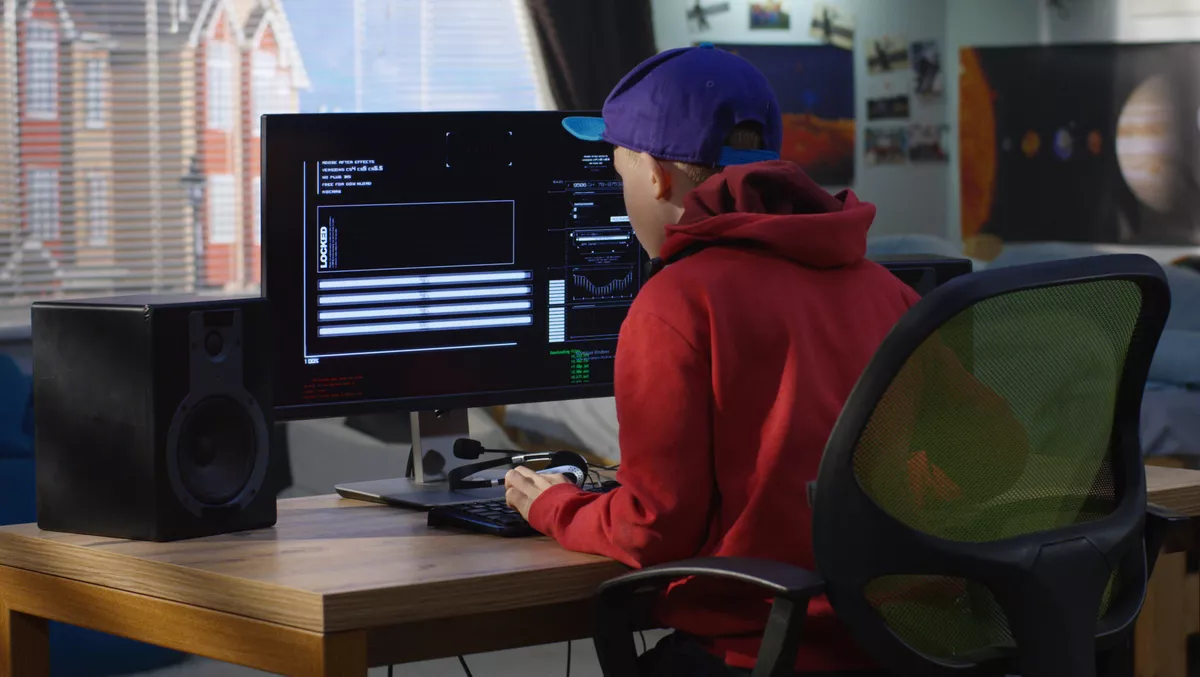
Minors using Discord servers to spread malware for cash
Wed, 20th Jul 2022
Digital security and privacy company Avast has discovered an online community of minors constructing, exchanging and spreading malware, including ransomware and a mix of information stealers and cryptominers.
Avast says the group lures young users by advertising access to different malware builders and tool kits that allow laypeople to construct malware easily. In some cases, people have to buy access to the malware builder tool to join the group, and in others, they can become group members where they are offered the tool for a nominal fee of AUD $7 to $37.
The community uses dedicated Discord servers as a discussion board and selling place to spread malware families such as Lunar, Snatch, or Rift, which follow the current trend of malware-as-a-service.
Avast says the discussion boards unveil that kids revealed their ages, discussed the idea of hacking teachers and their school systems and mentioned their parents in conversations. Findings show the ages of participants vary from 11 to 18-year-olds.
In a Discord group focusing on selling Lunar, there were over 1.5k users, out of which about 60-100 had a client role, meaning they paid for the builder.
The company says the types of malware exchanged among teens target minors and adults and have options that include password and private information stealing, cryptomining, and even ransomware.
For example, if a client buys a builder tool and chooses to use it for data theft, the generated sample will send any stolen data to that particular client who generated and distributed it. Or, if a client uses a tool to create a ransomware sample, the victim will be asked to send money to that particular client's crypto wallet.
Other prominent features include stealing gaming accounts, deleting Fortnite or Minecraft folders, or repeatedly opening a web browser containing adult content, apparently simply for the sake of pranking others.
Avast Malware Researcher Jan Holman says these communities may be attractive to children and teens because hacking is seen as cool and fun.
"Malware builders provide an affordable and easy way to hack someone and brag about it to peers, and even a way to make money through ransomware, cryptomining and the sale of user data," he says.
"However, these activities aren't harmless, they are criminal. They can have significant personal and legal consequences, especially if children expose their own and their families identities online or if the purchased malware actually infects the kids computer, leaving their families vulnerable by letting them use the affected device. Their data, including online accounts and bank details, can be leaked to cybercriminals."
Malware distribution via YouTube
Avast says after purchasing and compiling their individualised malware sample, some clients use YouTube to market and distribute their malware. For example, the company's researchers have seen clients create a YouTube video supposedly showing information about a cracked game or game cheat, which they link to. However, the URL leads to their malware instead.
To create trust around the video, they ask other people on Discord to like and leave comments under the video, endorsing it and saying it is genuine. In some cases, they even asked others to comment that if their antivirus software detects the file as malicious, it's a false positive.
"This technique is quite insidious, because instead of fake accounts and bots, real people are used to upvote harmful content. As genuine accounts are working together to positively comment on the content, the malicious link seems more trustworthy and, as such, can trick more people into downloading it," says Holman.
Through monitoring the online communities, Avast discovered that despite group members supporting each other with cybercrime partially meant as pranks, there was also information and money stealing, and conversations quickly became quite turbulent.
A considerable amount of fighting, instability, and bullying amongst users with cutthroat competition that goes to the point of appropriating someone else's codebase and slandering them was observed.
Avast says it reached out to Discord to inform them about these groups, and Discord confirmed they take action to address these types of communities and has banned the servers associated with Avast's findings.