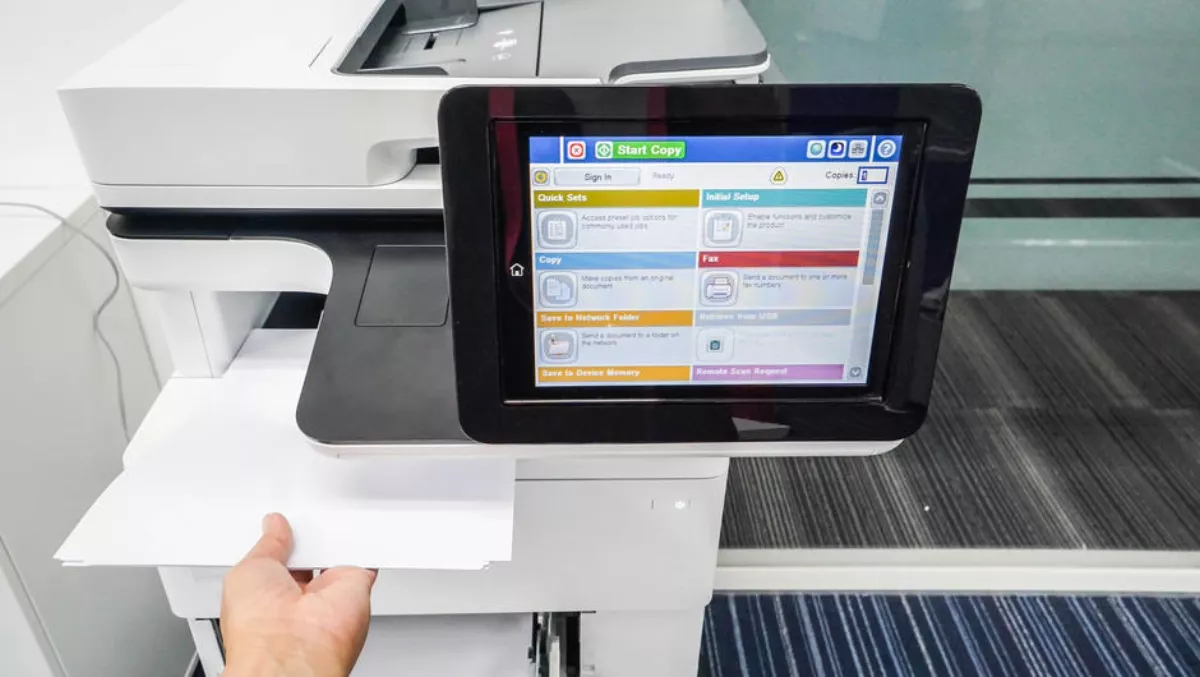
Multifunction devices such as printers and office machines are more commonly part of the Internet of Things as organisations look to increase value and office productivity. But are those devices secured against threats?
Organisations should consider new innovations to secure print device access, according to Y Soft. The company's Australian managing director, Adam O'Neill, says the industry plays a part in making that happen.
“What this means is that the industry needs to look at how to help organisations secure access to these valuable devices. Additionally, government regulations with painful financial consequences make security and data privacy a higher than ever requirement,” he explains.
Until recently, organisations have had a few different options such as usernames and passwords for accessing print management software and ID badges for card readers. Print management software in the multifunction device would then verify credentials against a corporate directory.
“Companies are asking for more alternatives, whether that's because they have an inherent need for a high level of security or a desire to make access more secure, while not so difficult that users devise ways to circumvent the security,” O'Neill adds.
So what kinds of technologies are available? Y Soft says there are a number of user identification methods that are gaining traction.
1. Cloud and mobile authentication. With the growing adoption of Windows 10 and Windows Hello for Business, cloud-based delivery for identity verification is possible. Whether verifying against an on-premise Active Directory or Azure Active Directory, the password is replaced by a two-factor authentication tied to a device by a biometric or PIN.
For mobile devices, there is a shift toward out of band (OOB) authentication. An example is a networked-based push notification requiring the user to enter a code or a push notification combined with an additional authentication that the user must possess.
Networked print devices might involve a mobile push notification that provides a passcode as a second method for access. The additional method requires storage of the user-defined piece of knowledge, a sensor or technology to support tokens. 2. Adaptive access. Most will recognise adaptive access as it is common in online banking. Adaptive access uses a set of rules and information to assess risk.
These might include information about the user, the type of device, time of day, device location, and the type of access requested. If the risk is deemed too high, access is denied and the user must prove identity through additional layers or methods. For networked printers for example, access requests during off-hours might require additional security layers. 3. Biometrics. Facial recognition and fingerprints are already common for securing access to smartphones. It is not difficult to see how that technology can transfer to networked office equipment such as MFDs.
The key to biometrics is the need to capture a sample, or baseline, of the trait and to extract data from it in a way that preserves its uniqueness. It has to be persistent and be measurable. As we see with facial recognition and fingerprints on smartphones, sensors are becoming more reliable. An important consideration for organisations considering biometrics is that biometric traits are personally identifiable information and, therefore, subject to privacy regulations. As such, the data collected has to be viewed as sensitive information.
“While some of the biometric methods may seem out of a science fiction movie, they are likely coming to organisations soon. With the adoption of home assistants such as Amazon Alexa and Google Home, voice recognition is already on its way to be integrated with multiple types of applications. Similarly, facial recognition and fingerprint scans are quickly being developed as reliable methods on smartphones. The jump to office networked devices is already happening,” O'Neill says. “As a rule of thumb, security experts recommend the choice of identity verification method be balanced with costs, risks associated with access, technologies required, and the user experience (UX).
