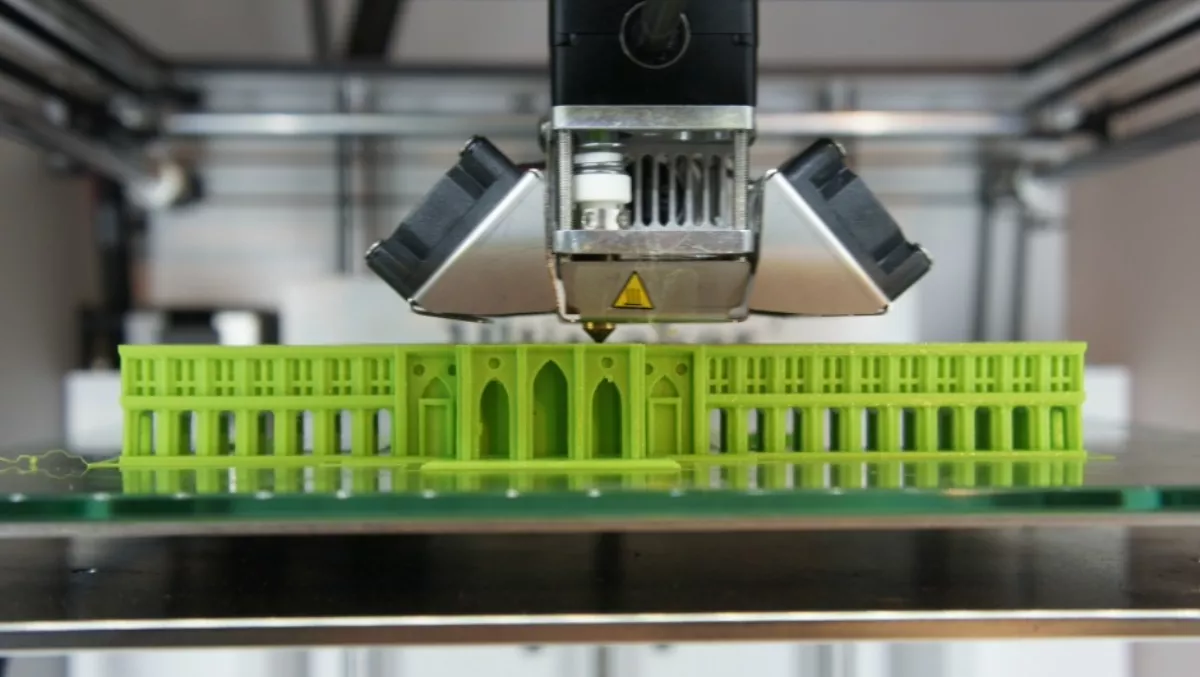
A team of researchers has recently reported cyber security risks in 3D printing.
Their discovery was found by examining two aspects – printing orientation and insertion of fine defects.
The findings were published in the journal of the Minerals, Metals and Materials Society by Mechanical Engineering. Essentially, they were based on the fact that because Computer-Aided Drafting (CAD) files – used in the analysis, modification or optimisation of a design – don't give instructions for the printer-head orientation, malefactors could alter the process without being detected.
This isn't to mention that sub-millimetre defects between printed layers with exposure to fatigue and the elements were also found to be undetectable
"These are possible foci for attacks that could have devastating impact on users from the end product, and economic impact in the form of recalls and lawsuits," says Nikhil Gupta, an associate professor of Mechanical Engineering. "Minus a clear directive from the design team, the best orientation for the printer is one that minimises the use of material and maximises the number of parts you can print in one operation," he said.
According to their research, the orientation of the product during printing could make as much as a whopping 25 percent difference in its final strength.
Said Karri, a cyber security researcher, affirms that in the increasingly digital world, there are more and more backdoors for malicious activity. Provided the printer is connected to the Internet, hackers can make their way in and introduce internal defects as the component is being printed.
"With the growth of cloud-based and decentralised production environments, it is critical that all entities within the additive manufacturing supply chain be aware of the unique challenges presented to avoid significant risk to the reliability of the product,” Karri concludes.