Ransomware infection? Here's how you control the damage
Mon, 12th Nov 2018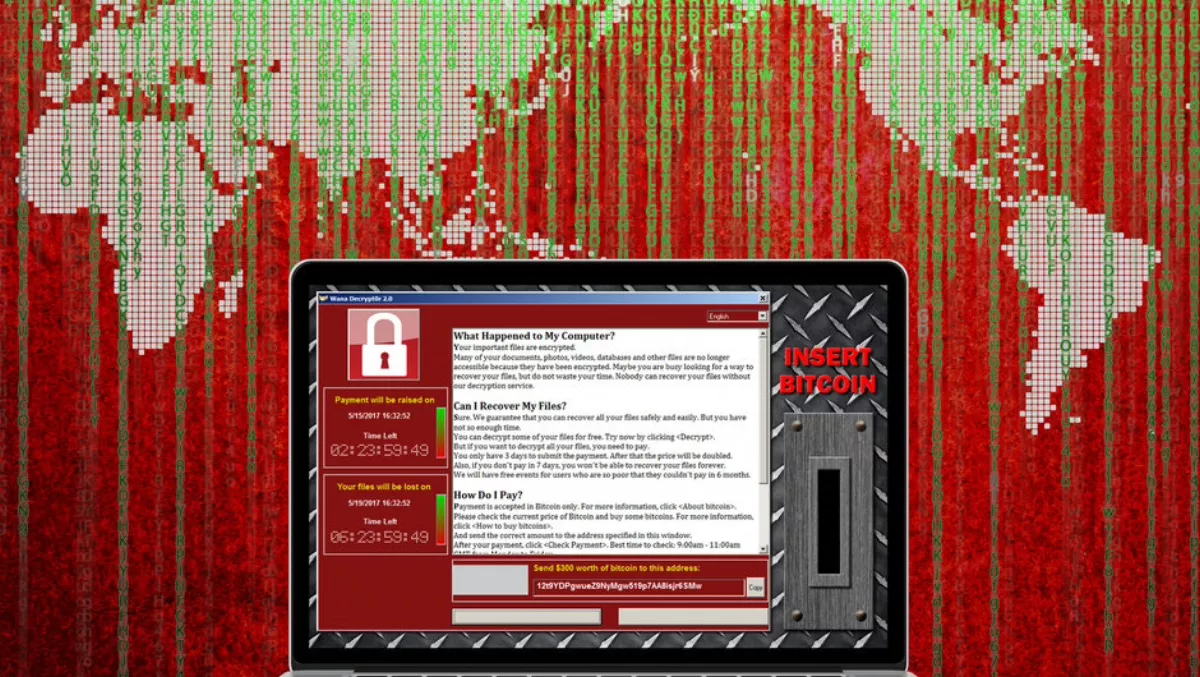
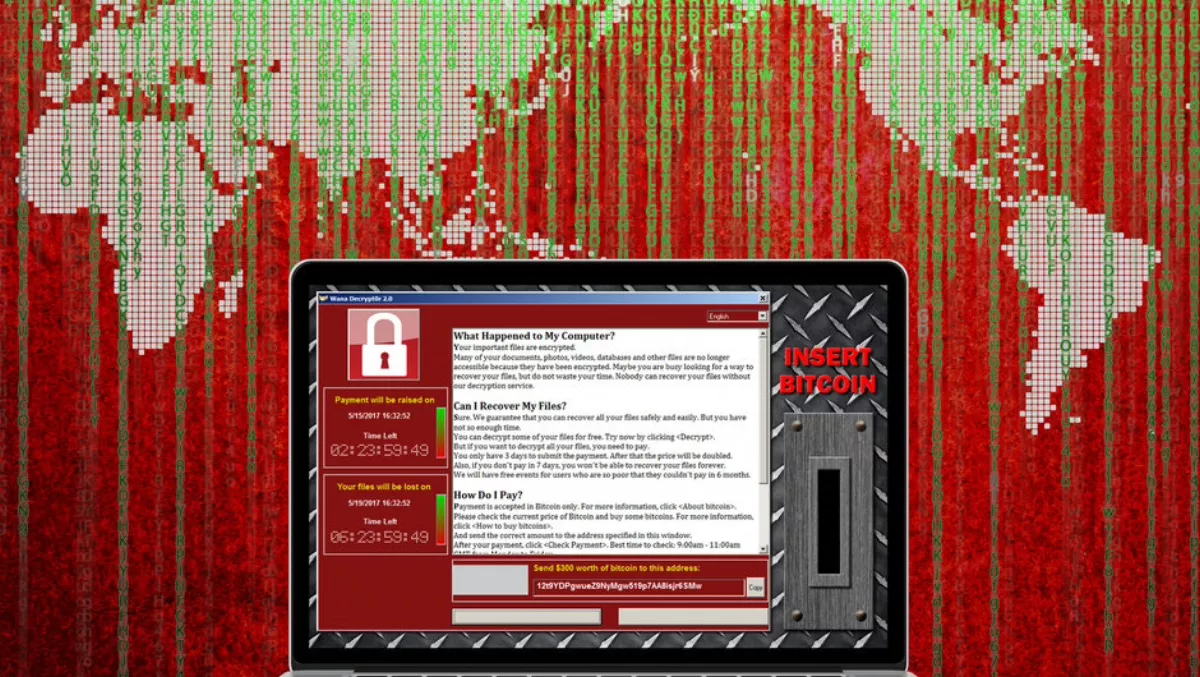
Eighteen months ago, ransomware hit headlines around the world with the WannaCry and Petya outbreaks which spread across 150 countries.
Since then, cryptojacking and other types of cyber threats grabbed headlines while ransomware incidents declined.
While the lower attack volume may suggest that file-encrypting ransomware is no longer a risk, that's not the case.
Ransomware has evolved to be more sophisticated, crafty and targeted and remains a threat to businesses of all sizes.
A case in point is GandCrab which kicked off 2018 with a flurry.
Since its January debut, new versions of the ransomware have been released as soon as a decryptor is developed.
Using the ransomware-as-a-service (RaaS) model, the cybercriminals behind GandCrab concentrate on development and take a cut of the proceeds letting others with lesser technical skills run the campaigns.
Infection estimates to date are at nearly half a million victims globally with recent incidents reported in Australia.
In late September, the Australian Cyber Security Centre reiterated the need for Australian businesses to remain vigilant of ransomware and the damage, both reputational and financial, it can cause.
Without access to their files and data, a business can be crippled for days.
Their clients may no longer trust the business to keep the clients' data secure. Moreover, with the introduction of the Notifiable Data Breach (NDB) scheme and the EU General Data Protection Regulation, businesses can also potentially face significant fines for non-compliance.
Small-to-medium businesses (SMB) tend to assume that their business is too small to be a target.
Rather, SMBs are soft targets for cybercriminals.
According to the latest Commonwealth's Stay Smart Online Small Business Guide, 59% of Australian organisations have their business interrupted by a cyber breach every month, and 43% of all cybercrime targets small business.
Generally, SMBs have less-sophisticated security programs in place and are unlikely to have IT or dedicated IT security staff to manage and respond to cyber threats.
Of course, preparation is always better than response.
There are many sources for steps to prevent ransomware in the first place including advice on the Commonwealth's cyber.gov.au site.
However, if a business does fall victim to a ransomware attack, the advice from law enforcement agencies across the globe is never to pay a ransom.
Disconnect the infected systems from network access
Ransomware like WannaCry contain routines for spreading across the network. Isolate the infected devices from all, wired and wireless, network connections.
However, do not turn the infected computer(s) off.
Doing so risks removing criminal evidence as well as possibly removing critical files which could be used to decrypt.
Check what type of ransomware infected your systems Take a picture of the ransomware message screen.
Security researchers have created web-based portals to help users by providing basic information on existing ransomware.
Two of the sites worth mentioning is ID Ransomware and No More Ransom Project.
Both sites can help identify the ransomware that hit your systems and whether there are readily available tools to decrypt the infected files.
Check if the files can be recovered
Modern Windows OS, by default, saves the previous states of the system in case of breakdowns or BSOD (blue screen of death) errors.
Check if the previous state of the system can be restored using System Restore Point or Volume Shadow copies.
Note that some destructive ransomware such as WannaCry, Locky and Cryptolocker also delete these system snapshots to make recovery of files more difficult.
Locate the backups
Some computer devices pre-installed with Windows or Mac OS when purchased may have been set to backup automatically in a recovery drive or in the cloud.
Check for these functionalities and how it can help recover the infected files.
If the files are backed up on an external hard drive, avoid connecting it to the ransomware-infected device as it is still active, and the backup files can be encrypted.
As best practice, SMBs are recommended to follow the 3-2-1 backup strategy on making data resilient against ransomware attacks.
This strategy takes three copies of the data, stored in at least two different mediums with one copy stored in a location not accessible on the internet.