Petya ransomworm's rapid spread: What the experts know right now
A 'virulent' variant of a ransomworm dubbed 'Petya' is spreading across multiple countries including Ukraine, Europe and the United States is hitting businesses in energy, banking and transport, and consumers too. There are yet to be reports of appearing in Asia Pacific, but that doesn't necessarily mean it won't infect the region.
This malware appears to have been targeted to Ukraine infrastructure groups such as government workstations, power companies, banks, ATMs, state-run television stations, postal services, airports, and aircraft manufacturers. Since the initial infection it has spread to other markets, and beyond the Ukraine boarders," comments Ivanti's CISO, Phil Richards.
Although the ransomware has been around a few months, McAfee says it's different from others because it is able to encrypt files and an operating system's master boot record.
The master boot record is critical to a system's startup processes and if the trojan spread that far, the entire drive suddenly becomes encrypted - not only the system files.
"It's critical to note that the email address associated with this ransomware has been deactivated, and so infected organizations should not pay the ransom under any circumstances," says Proofpoint's Ryan Kalember, SVP CyberSecurity Strategy.
The strain currently infecting systems this week also uses the EternalBlue exploit as part of its infection process, much like the WannaCry ransomware that inflicted major damage on systems earlier this year.
A statement from Fortinet says that like WannaCry, Petya fits into the new breed of 'ransomworm' as it moves across multiple systems automatically, rather than staying in one place.
"If this attack turns out to be leveraging the same vulnerabilities WannaCry leveraged to spread, or other known bugs that have had patches available for months, there are going to be some awkward conversations between IT teams that failed to patch or protect and businesses affected. The publicity around WannaCry couldn't have been larger, probably eclipsing Heartbleed, yet if this is the same attack vector, it demonstrates a distinct lack of taking threats like this seriously, comments Tenable's technical director Gavin Millard.
Kobi Ben Naim, senior director of cyber research, CyberArk Labs is dubbing the new variant 'NotPetya'.
"Based on initial analysis by CyberArk Labs, what we know now is that NotPetya is different from WannaCry in that it appears to be sparing endpoints that use a US English-only keyboard," Ben Naim says.
ESET has also pinpointed the origin of the attack; speculating that attackers compromised accounting software M.E.Doc and infected it with a trojanised update. M.E.Doc is a popular platform in Ukraine.
FireEye reports that the M.E.Doc website is down, with a message in Russian confirming it is under attack.
However Fortinet believes that this latest attack started through distribution of an Excel document that takes advantage of a known Microsoft Office exploit.
Symantec says that at this stage it is not clear if the Petya ransomware is part of a targeted attack. Previous strains have been used in targeted attacks in the past.
Sophos says that ""The exploit attacks vulnerable Windows Server Message Block (SMB) service, which is used to share files and printers across local networks. Microsoft addressed the issue in its MS17-010 bulletin in March, but the exploit proved instrumental in the spread of WannaCry last month. The new Petya variant can also spread by using a version of the Microsoft PsExec tool in combination with admin credentials from the target computer.
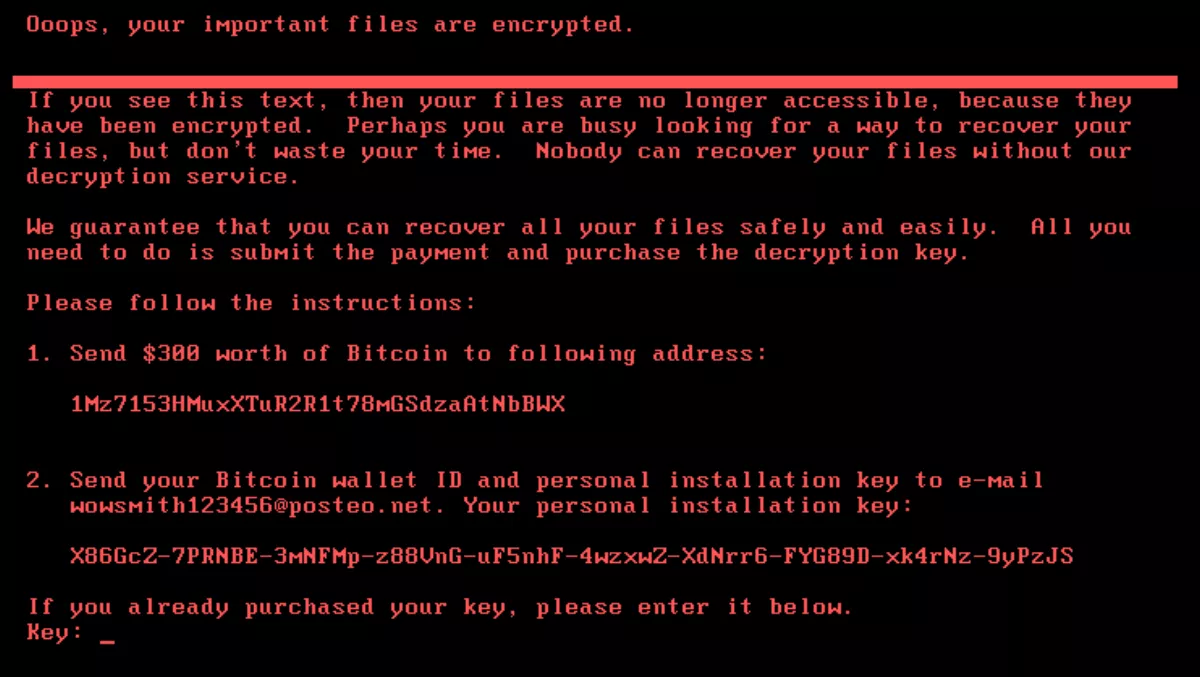
ESET researchers also translated the ransom message and discovered that the attackers are looking for 300 bitcoins to buy back the encryption key. However as Proofpoint mentioned, the email address has been deactivated and it is warning users not to pay the ransom.
Palo Alto Networks' Unit 42 researchers also found that the Petya ransomware contains no command and control mechanisms - which means there is no communication between the ransomware and the attackers.
"Neither businesses nor individuals should pay ransoms to unlock any files that have been affected by a ransomware attack, as this incentivises and rewards these kinds of attacks. In order to prevent becoming a victim of a ransomware attack, data should be backed-up and encrypted, and stored away from the network the rest of the data is stored on," comments Graeme Pyper, Gemalto's ANZ regional director.
Although security firms are saying Petya is not quite as severe as WannaCry, but the similarities between the two are significant.
Malwarebytes believes that Petya has also been heavily influenced by the original Petya malware, although this has not been confirmed.
"Petya/ NotPetya is another example of a know, patchable vulnerability causing tremendous issues for people and businesses around the world. If possible apply MS17-010 Microsoft patch to all PCs immediately," adds Malwarebytes ANZ regional director Jim Cook.
ESET warns that all it takes is one unpatched computer for the ransomware to get inside the network. It is warning all users to make sure their patches are up to date. ESET is also offering the EternalBlue Vulnerability Checker as a download for those who want to make sure.
"The recent attacks associated with WannaCry and Petya have re-enforced the lack of accountability and focus on basic IT and security fundamentals. Core IT operational competencies, such as patch management, backups, disaster recovery, and incident response are not well implemented or maintained," comments LogRhythm's VP and managing director of international markets, Ross Brewer.
Fortinet adds that there were additional attack methods and patching alone is not enough. It advises users to patch and use strong security tools and practices. Fortinet will be hosting a webinar for its customers on Thursday - details will be confirmed shortly.
CERTNZ also reminds organisations to raise staff awareness about the attacks and to be vigilant about email links and attachments.
Stay tuned to see what other leading security vendors are saying as the outbreak continues.


