Stories by Staff - Page 2

7 tech trends that define next-generation data center monitoring
Thu, 15th Jun 2017
#
bi
#
big data
#
cloud services
Automated monitoring has moved front and center as too few human resources are available to manage the large quantities of information coming in.

Redefining efficiencies for downsized, on-premise enterprise data centers
Thu, 15th Jun 2017
#
data centre cooling
#
data centre maintenance / management
#
power / energy
The industry is undergoing a third transformational phase: a retrenchment, and even a renewed growth, of enterprise on-premise data centers.

Schneider Electric: Challenges and trends in colocation
Tue, 13th Jun 2017
#
data centre maintenance / management
#
colocation
#
power / energy
Telco facilities typically have an ideal location, possess digital technology with connectivity in place and own central offices with available space.

E3 2017: Keeping gamers and games connected for the win
Fri, 9th Jun 2017
#
gaming
#
data centre operators
#
technology gifts
Achieving the ultimate interconnection between gamers and games with a high-quality user experience is what powers the $108.9 billion gaming market.

HPE’s next frontier: Space travel & memory-driven computing
Fri, 9th Jun 2017
#
smartphones
#
technology gifts
#
memory
By 2020, our digital universe will contain nearly as many bits of data as there are stars in the universe, with at least 20 billion mobile devices.
HPE: Jamshedpur, India - From steel city to smart city
Fri, 9th Jun 2017
#
iot
#
fleet management
#
hpe
Tata Communications, a provider of telecommunications solutions and services, has 44 data centers located around the world, including India.

Takeaways of a data center guy after Cloud Computing wins the Preakness
Fri, 9th Jun 2017
#
colocation
#
iot
#
data centre maintenance / management
Cloud Computing's Preakness win prompts a data centre insider's race to draw parallels with tech and risk management in the field.

Polycom case study: How remote working helped me adopt a lifestyle change
Thu, 8th Jun 2017
#
wfh
#
remote working
#
poly
Often when I tell others I work from home, they ask me how I stay motivated or not end up in front of the TV (or fridge) all day.

HPE: Stay on the cutting edge with software defined OT
Wed, 7th Jun 2017
#
iot
#
edge data centre
#
edge computing
As competition in the IoT and Intelligent Edge industries increases, companies are seeking new ways to stand apart and delight their customers.

WannaCry, IoT and you: Securing your customers in an unsafe world
Tue, 6th Jun 2017
#
firewall
#
malware
#
ransomware
Ingram Micro’s Andrew Khan explains how ransomware like WannaCry can be mitigated by the 3As: Automation, analytics and artificial intelligence.

Schneider Electric: Enhancing data center performance, gamefully
Sun, 4th Jun 2017
#
colocation
#
data centre maintenance / management
#
power / energy
Schneider Electric pioneers data centre gamification, promising efficiency gains and cost savings with innovative management tools.

New data center cooling tech - crucial to achieving carbon reduction goals
Fri, 2nd Jun 2017
#
colocation
#
data centre cooling
#
data centre maintenance / management
Countries around the globe are taking definitive steps to reduce greenhouse gas (GHG) emissions and, consequently, their carbon footprint.

Schneider Electric: The impact of the cloud on hybrid data center designs
Thu, 1st Jun 2017
#
cloud services
#
wfh
#
data centre maintenance / management
Cloud adoption is driving the need to rethink the redundancy requirements of edge data centers, says Kevin Brown of Schneider Electric.

The connected campus: Meeting students’ #1 priority with edge solutions
Thu, 1st Jun 2017
#
colocation
#
data centre maintenance / management
#
edge data centre
To stay alive, human beings need air, food and water. If you are college student, add to this list of vital resources Internet access.

DCIM’s improvement to workflow processes is key to eliminating data center challenges
Mon, 29th May 2017
#
data centre cooling
#
data centre maintenance / management
#
power / energy
But for me, the most interesting aspects of the research is in unpacking the impact of a range of data center problems on the business itself.

Why SD-WAN is the ‘killer app’ for NFV services
Mon, 29th May 2017
#
network infrastructure
#
network management
#
sd-wan
Silver Peak’s Graham Schultz takes a look at the recent NFV World Congress, and a new Silver Peak vCPE offering for service providers.

Equinix: Optimizing multicloud interconnection at the digital edge
Fri, 26th May 2017
#
colocation
#
iaas
#
dci
Multicloud solutions are the new norm for more organizations, with 85% of enterprises employing a multicloud strategy – 58% being hybrid clouds.

Why this new Gartner data center modernization report caught me by surprise
Thu, 25th May 2017
#
data centre maintenance / management
#
colocation
#
power / energy
Until now, I had always pictured colocation as a large warehouse for IT equipment and not a platform that would support smaller scale implementations.

Optimizing interconnection for hybrid apps is the key to greater customer experience
Wed, 24th May 2017
#
crm
#
contact centre
#
cloud services
The future of application design is not dependent solely on serverless, containers, microservices, bots or some completely new technology.

Data center modernization: A plan for how much to outsource
Wed, 24th May 2017
#
outsourcing
#
colocation
#
data centre maintenance / management
The spectrum for how to modernize an existing data center is quite wide, and the cost/benefit scenarios differ.

Schneider Electric: Water, water, everywhere, nor any drop to drink…
Tue, 23rd May 2017
#
big data
#
bi
#
network infrastructure
Data dyke breached: Schneider Electric reveals a flood of untapped savings lurking in our data centers.

You can’t burn it down and start over; how to modernize a data center in 4 steps
Mon, 22nd May 2017
#
data centre cooling
#
colocation
#
data centre maintenance / management
No matter what, there will come a time when a system is so outdated, there’s no amount of fixing that can help.

APIs – the key to collaboration between fintech and traditional finance institutions
Tue, 16th May 2017
#
accounting systems
#
fintech
#
digital banking
APIs provide the necessary security, governance, and scalability, while still allowing the rich enablement users require.
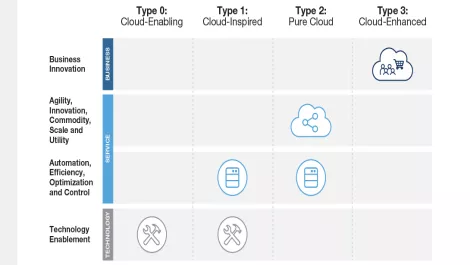
Breaking down cloud computing and its nuances - Gartner
Fri, 12th May 2017
#
cloud services
#
colocation
#
gartner
Cloud computing is often thought of as one technology, but organisations should consider which type of cloud computing is the most effective.